Background
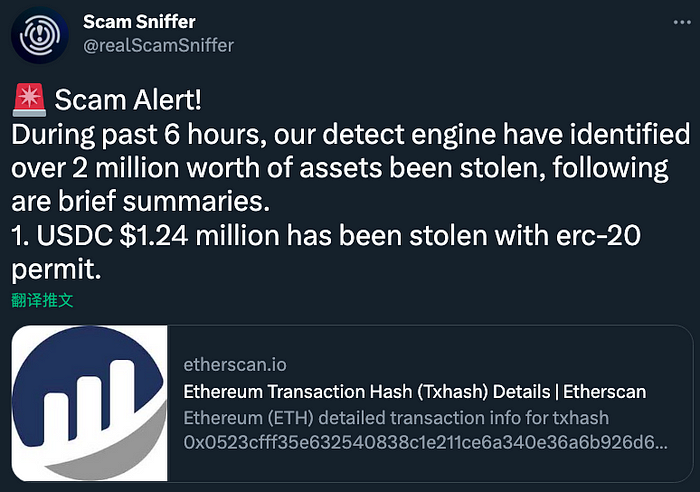
On February 8th, 2023, the SlowMist security team received a report from our partner ScamSniffer regarding multiple security breaches due to phishing attacks. An individual even suffered a significant loss, amounting to over $1.2M in USDC.
Hacker Address: 0x69420e2b4ef22d935a4e2c194bbf3a2f02f27be1
Profit Address: 0x9cdce76c8d7962741b9f42bcea47b723c593efff
As for the broader picture of phishing attacks, our team made its first global disclosure on December 24th, 2022, regarding the “Investigation of North Korean APT’s Large-Scale Phishing Attack on NFT Users”. This particular phishing incident is linked to another group known as Monkey Drainer, which we have been closely monitoring. While we have conducted a thorough analysis of some of the phishing materials and wallet addresses used by the group, we have chosen to keep certain details confidential due to privacy and confidentiality concerns.
Analysis of Phishing Websites
After conducting a thorough investigation, it was discovered that the primary tactic utilized in this phishing attack was the creation of counterfeit NFT-related websites through fake celebrity Twitter accounts and Discord groups. These NFTs were then sold on platforms such as OpenSea, X2Y2, and Rarible. The Monkey Drainer organization aimed their attack at Crypto and NFT users, using nearly 2,000 different domains.
By checking the registration information of these domain names, we found that the earliest registration date can be traced back to 4 months ago.
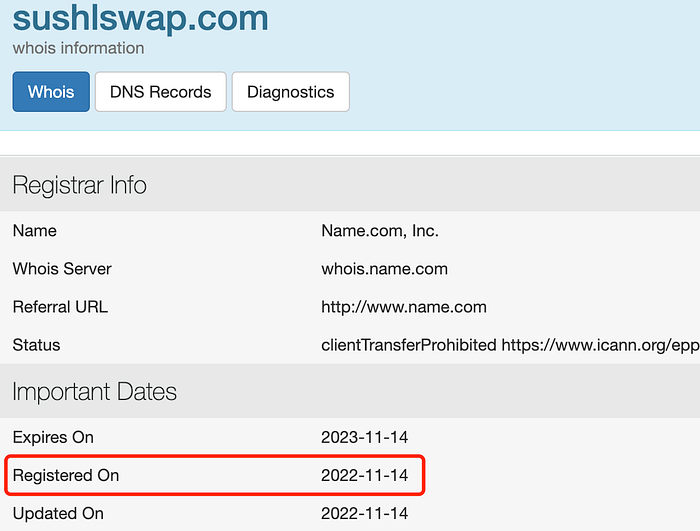
Initially, the Monkey Drainer organization spread their phishing campaign through false promotions on Twitter.

Meanwhile, the first NFT phishing occurred: mechaapesnft[.]art
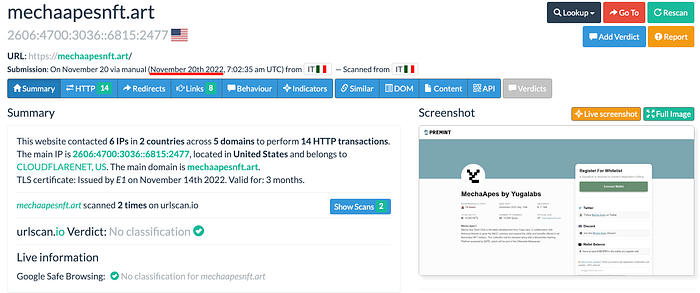
Let’s look at two specific associated traits:

We track through a combination of traits:
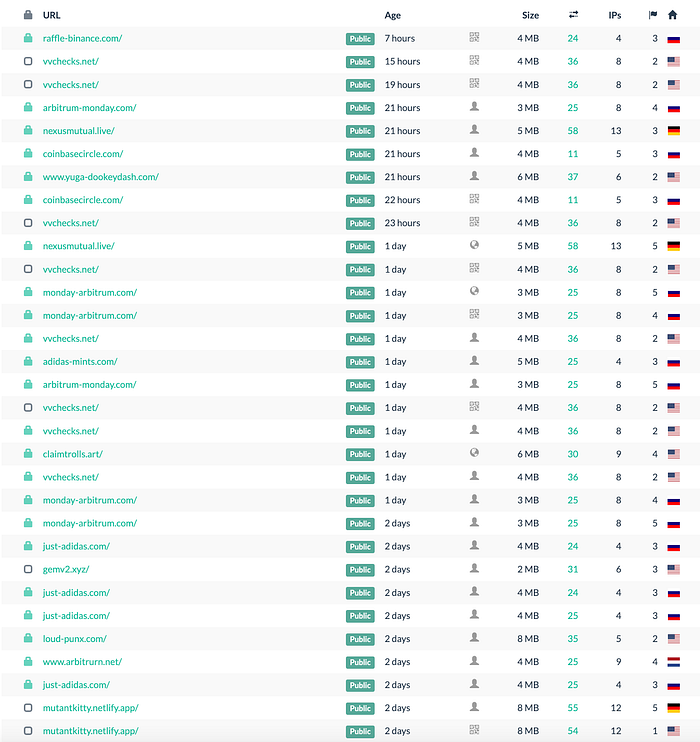

Our team was able to uncover over 2,000 NFT phishing websites and related domains that share similar characteristics from the year 2022 until now.
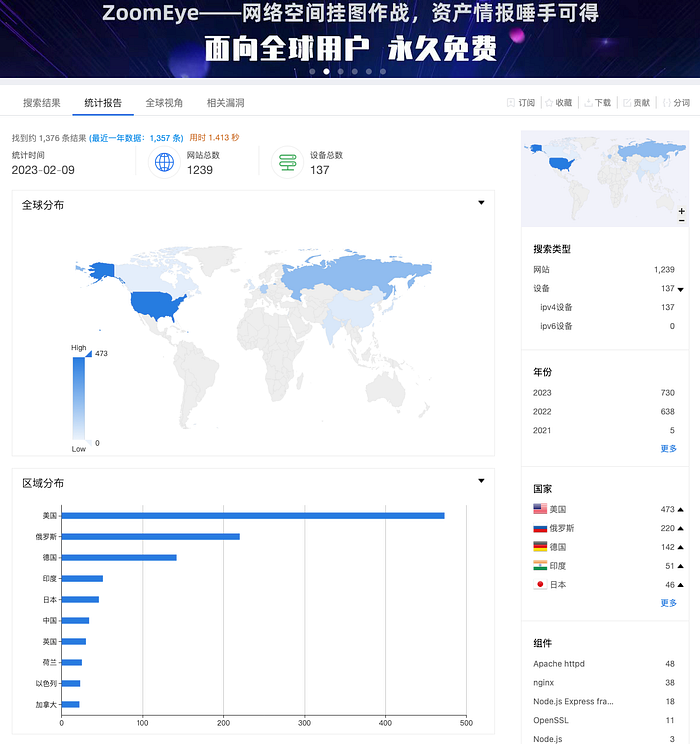
To determine the current state of these phishing sites, we employed the use of ZoomEye to conduct a comprehensive global search. The results of our investigation revealed the staggering number of active and operational phishing sites.:
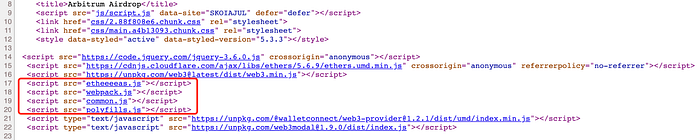
For example, the latest scam was disguised as an Arbitrum airdrop:


In contrast to the North Korean hacking organization, the Monkey Drainer phishing group does not possess the capability to track the records of victims visiting each site through a dedicated website. Instead, they employ a straightforward and brutal method, resorting to direct phishing and mass deployment. It is assumed that the Monkey Drainer phishing group uses phishing templates to automate batch deployment.
As we delved deeper into the investigation of the supply chain, we uncovered that the Monkey Drainer NFT phishing group relied on a pre-existing gray market for their infrastructure. Specifically, they utilized a template that was readily available for sale in the form of advertisement descriptions.
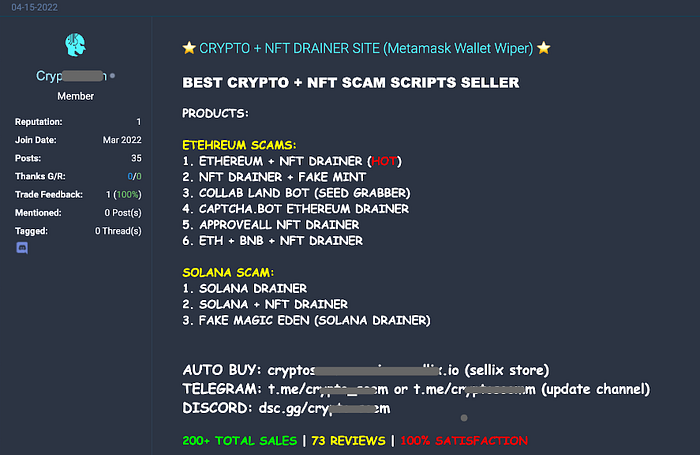
Supported functions in the phishing supply chain:
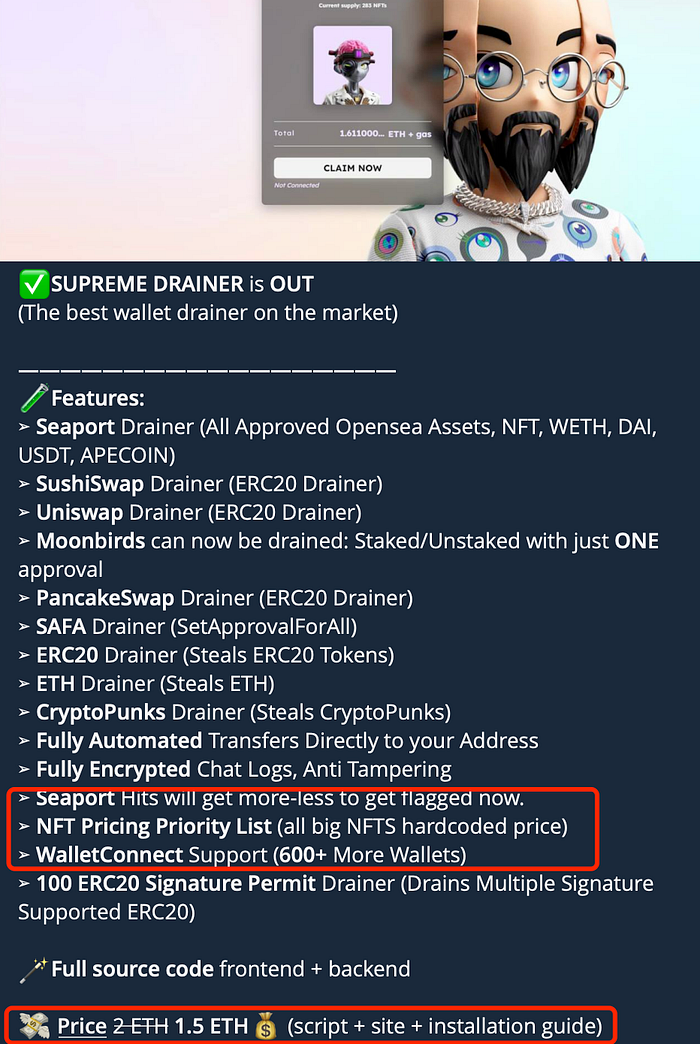
Based on the information provided in the introduction, the offer includes competitive prices and a wide range of features. However, due to limited space, we will not delve further into this topic at this time.
Analysis of Phishing Methods
Together with the previous “How Scammers Are Paying Nothing for Your NFTs” report released by SlowMist, we have conducted an analysis of the core code involved in this phishing incident.
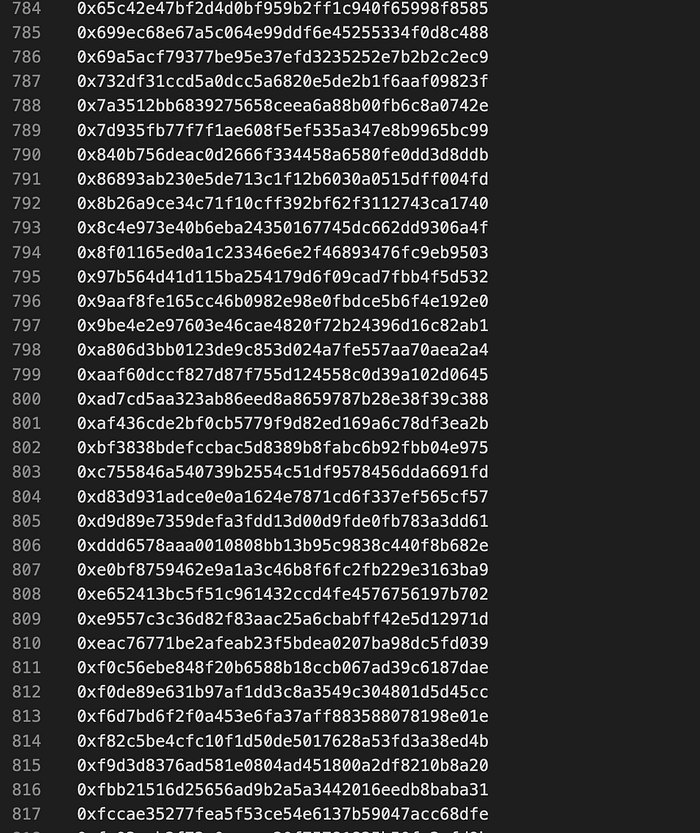
The core code incorporates obfuscation techniques and manipulates victims into signing Seaport, authorizations, and other signatures.

The incorporation of an offline authorization signature mechanism for allowing USDC, among others, elevates the original phishing mechanism.
Here is an example of a fraudulent signature referred to as “SecurityUpdate”.\:

In a more readable format:
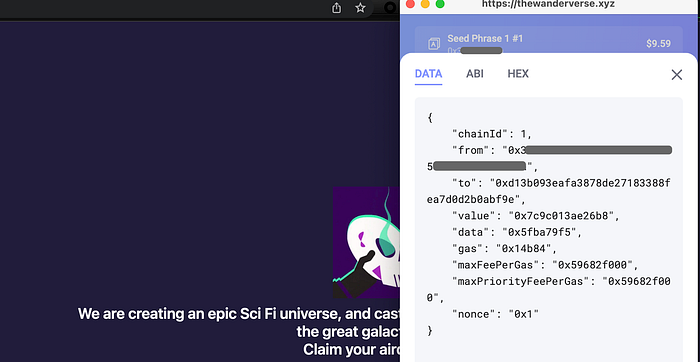
The Rabby plugin wallet’s data analysis and visualization has been thoroughly performed and presented in a clear and easily understandable format. Further analysis will not be detailed here.
Overview on chain
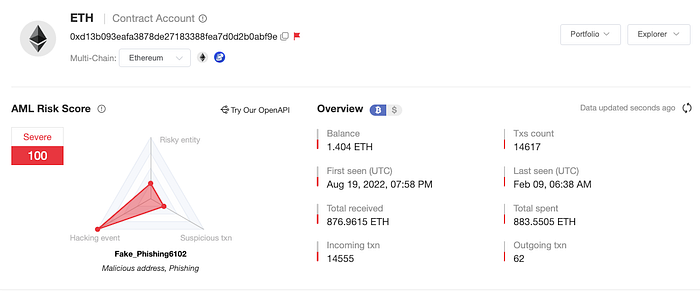
Based on the analysis of over 2,000 phishing websites and the SlowMist AML malicious address library associated with them, a total of 1,708 malicious addresses linked to the Monkey Drainer NFT phishing group were analyzed, with 87 of them being original phishing addresses. These relevant malicious addresses have been recorded on the MistTrack platform and the SlowMist AML malicious address database.
Tracking Analysis
Based on the analysis of the 1708 malicious addresses related to the Monkey drainer NFT phishing group, we were able to draw the following conclusions:
- Timeframe: The earliest identified set of active on-chain addresses dates back to August 19, 2022 and remains active up to the present time.
- Sample phishing transactions: 1, 2, 3
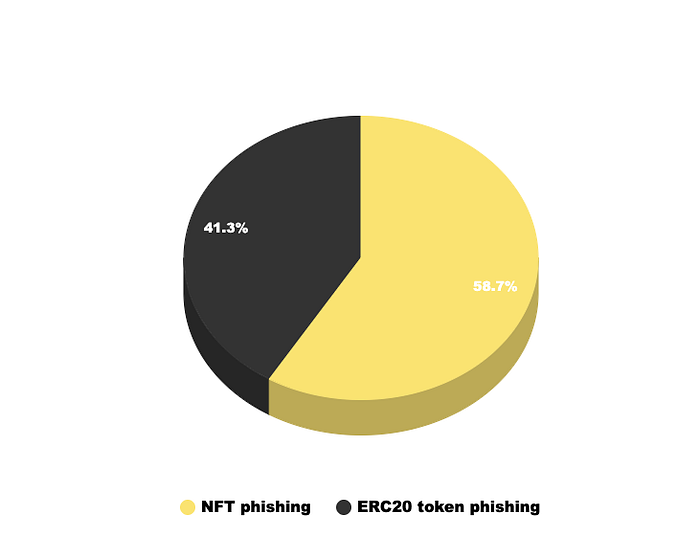
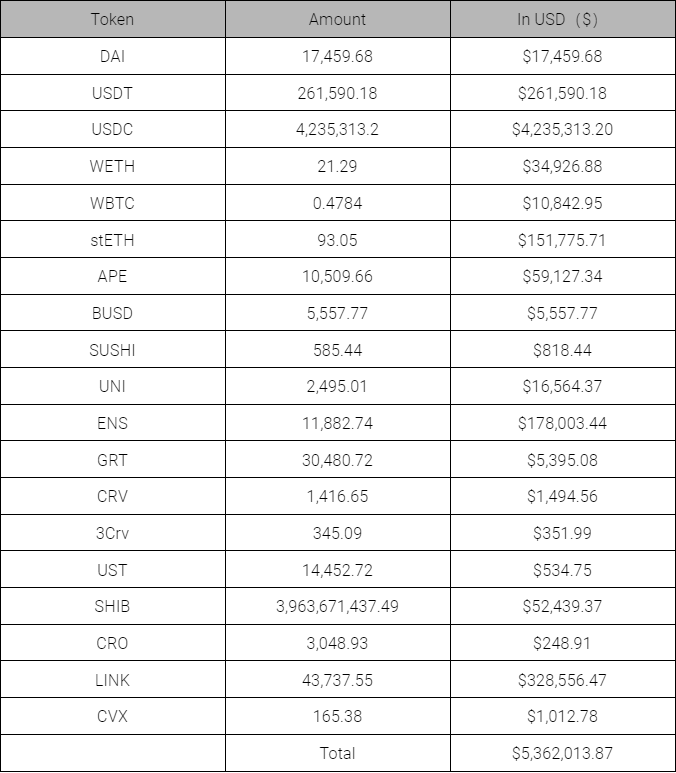
- Amount Stolen: The overall profit generated through phishing is estimated to be around $12.972 million. 7,059 NFTs were successfully phished, resulting in a profit of 4,695.91 ETH, equivalent to approximately $7.61 million, which represents 58.66% of the total funds acquired. The ERC20 Token profit was about $5.362 million, accounting for 41.34% of the funds gained, with the major ERC20 Token profits being from USDC, USDT, LINK, ENS, and stETH. (Note: ETH prices were obtained on 2023/02/09 from the data source CryptoCompare.)
Details of stolen ERC20 tokens:
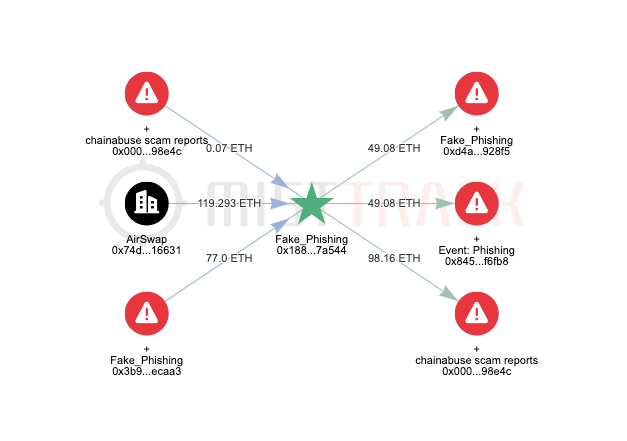
MistTrack Analysis
Our MistTrack team meticulously carried out a thorough on-chain analysis of the malicious addresses, and depicted the transfer of funds in a clear and easy-to-understand manner below.
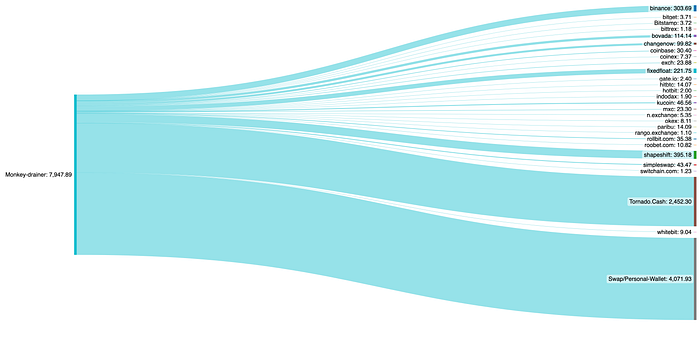
Based on the Sanky diagram, a total of 3,876.06 ETH of the profits was traced as being transferred to physical addresses, with 2,452.3 ETH being deposited into Tornado Cash, while the remaining funds were sent to various exchanges.
The source of the fees for the 87 initial phishing addresses is shown below.
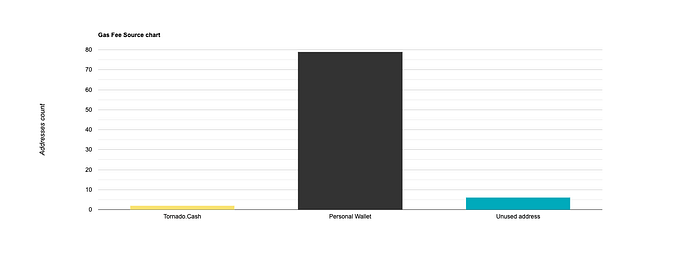
As depicted in the fee source histogram, two addresses received fees from Tornado Cash, while 79 addresses received transfers from personal addresses. The remaining 6 addresses, however, did not receive any funds.
Example
On February 8, the hacker’s address 0x69420e2b4ef22d935a4e2c194bbf3a2f02f27be1 gained access to the victim’s address throught a sophiscated phishing attack and stole over $1,200,000. They transferred 1,244,107.0493 USDC to 0x9cdce76c8d7962741b9f42bcea47b723c593efff, then exchanged the USDC for ETH through MetaMask Swap. A portion of the ETH was transferred to Tornado Cash, while the remaining funds were transferred to previously used phishing addresses.


Hackers Profile Analysis

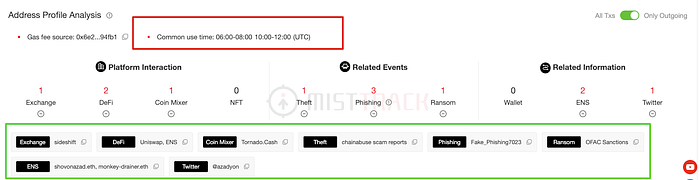
It was discovered that some of the funds obtained through the phishing attack were held at the original address, while others were transferred to Tornado Cash, as evidenced by on-chain analytics.
A big thank you to ScamSniffer and NFTScan for their support.
Summary
We examined a common NFT phishing approach to uncover a large-scale NFT phishing group associated with the Monkey Drainer organization and to extract the phishing characteristics of the Monkey Drainer organization. As Web3 technology evolves, the phishing methods against Web3 become more varied, putting users in a challenging situation.
It is crucial for users to assess the risk level of the target address prior to executing transactions on chain. This can be achieved by inputting the target address into MistTrack and reviewing its risk score and malicious labels, which helps to minimize the likelihood of financial loss.
For the wallet projects, it is necessary to conduct a comprehensive security audit at first, with a focus on improving the security of user interaction, strengthening the What you see is what you sign mechanism, and reducing the risk of users being phished, such as:
- Phishing Website Alert: Gather all kinds of phishing websites through the power of ecosystem or community, and prominently remind and warn of risks when users interact with these phishing websites.
- Signature Recognition and Alert: Identify and remind requests for signatures such as eth_sign, personal_sign, and signTypedData, and focus on reminding eth_sign of the risk of blind signing.
- What you see is what you sign: The wallet can implement a detailed analysis mechanism for contract calls to prevent Approve phishing and let users know the details of DApp transaction construction.
- Pre-execution mechanism: The transaction pre-execution mechanism can help users understand the effect of transaction broadcast execution, and aids in predicting the execution of transactions.
- Scam alert with the same ending number: When displaying the address, a noticeable reminder prompts users to thoroughly check the target address to avoid scams with similar ending number. Set up the whitelist address mechanism, users can add commonly used addresses to the whitelist to avoid attacks similar to the same ending number.
- AML Compliance Alert: During the transfer, the AML mechanism is used to remind the user whether the target address of the transfer will trigger the AML rule.
SlowMist, as a leading blockchain security company with years of expertise in security audits, not only provides peace of mind for users but also serves as a deterrent against potential attacks. Additionally, institutions face huge challenges in anti-money laundering efforts due to data silos, making it difficult to identify cross-institutional money laundering syndicates. For project stakeholders, it’s equally important to promptly blacklist and disrupt the transfer of funds from malicious addresses. Our MistTrack Anti-Money Laundering Tracking System has accumulated over 200 million address labels, enabling the identification of wallet addresses from major global trading platforms, including over 1,000 address entities, over 100,000 threat intelligence data, and over 90 million risk addresses. If needed, you can contact us to access our API. Lastly, we hope that all parties will work together to make the blockchain ecosystem a better place.